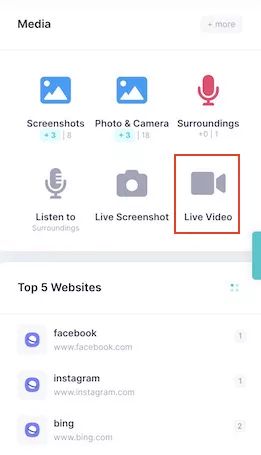
WHY IS IT USEFUL TO Watch the live screen?
The feature of recording phone screen to videos provides you with a visual video of exactly what the user is doing on Android phones and iPhone, which plays an important role in parental control and employee monitoring. Using iKeyMonitor remote phone screen recorder, you can know what your children are doing on their devices and whether they need your guidance and help. You can also easily know whether employees are conducting inappropriate activities on company-offered devices so as to prevent more serious problems and economic losses.
Watch The Screens of Children's Phones in Real Time
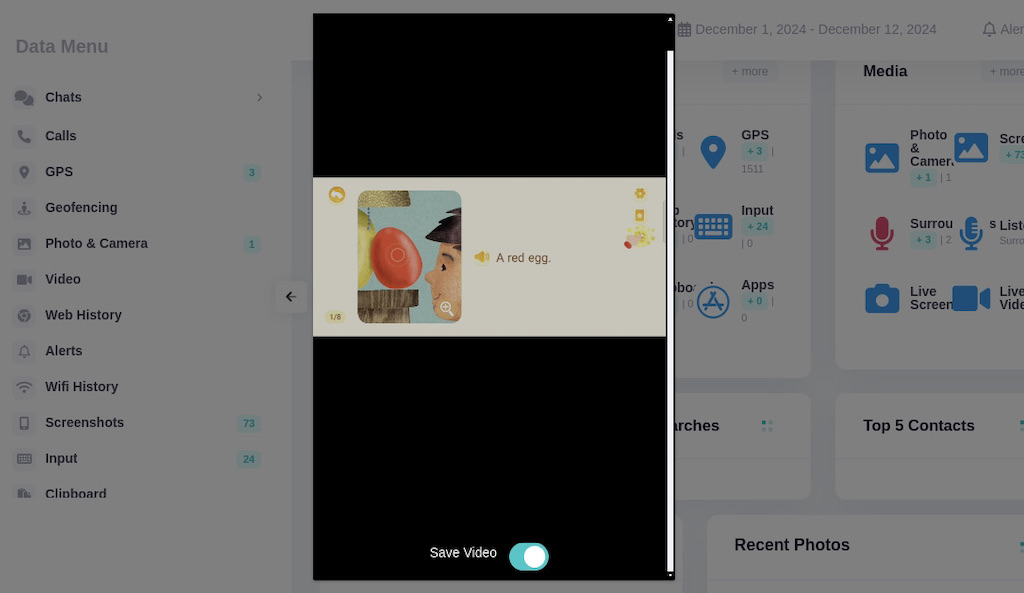
Watching the live screen video streams allows you to monitor your children’s phone activities in real time. For example, you can see what files they sent and received, which videos they watched, what emojis they sent, and all other activities that happened on their phone. Watching the whole screen activities ensures that you won’t miss anything important.
So, you can determine whether they are making friends with malicious people or whether they have received inappropriate messages from predators or friends, such as porn, bullying, threatening, harassment, or assault. Recording the phone screen as a video remotely helps you know what your children were doing from all aspects.
Watch The Screens of Employees' Phones in Real Time
Watching live screens also plays an important role in monitoring employees’ activities and performance at work. During work hours, some employees may use company-provided devices to conduct activities unrelated to their work, such as watching videos or films, shopping online, and video chatting with friends and family. Using a remote phone screen recorder to record employees' screens on the company devices shows visually which employees are just wasting the company’s resources and money.
Furthermore, some unethical employees may violate the company’s regulations and rules, such as selling or leaking trade secrets to competitors. iKeyMonitor is a free remote screen recorder that is capable of viewing multiple phone screens in real-time so that you can quickly and easily catch insider threats in a company. Additionally, the recorded screen videos can serve as persuading proof to support investigative in the future.